How do I decode a bearer token in node JS?
- import jwt_decode from "jwt-decode";
- var token = "eyJ0eXAiO...";
- var decoded = jwt_decode(token);
- console. log(decoded);
- Navigate to the Decrypt Tool section of the Token Auth page.
- In the Token To Decrypt option, paste the desired token value.
- In the Key to Decrypt option, select the encryption key used to generate that token value.
- Click Decrypt. The requirements for that token will appear next to the Original Parameters label.
- Struture of the JWT Token. A JWT Token looks as follows. ...
- Split the JWT Token. The token received in the request must contain 3 parts we mentioned above. ...
- Base64 Decode. ...
- Parse the JSON. ...
- Check the Expiry Timestamp. ...
- Verify the Signature. ...
- Access User information from Payload. ...
- Reference.
By design, anyone can decode a JWT and read the contents of the header and payload sections. But we need access to the secret key used to create the signature to verify a token's integrity.
Each JWT contains a payload. The payload is a base64 encoded JSON object that sits between the two periods in the token. We can decode this payload by using atob() to decode the payload to a JSON string and use JSON. parse() to parse the string into an object.
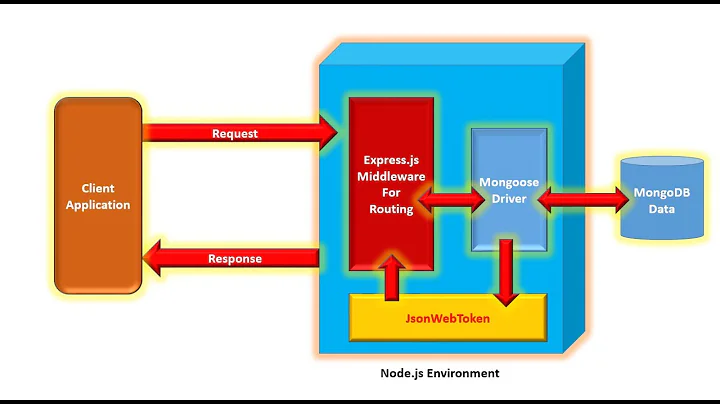
To authenticate a user, a client application must send a JSON Web Token (JWT) in the authorization header of the HTTP request to your backend API. API Gateway validates the token on behalf of your API, so you don't have to add any code in your API to process the authentication.
- Create our project: To create a Node project, npm init -y is used in the folder in which the user wants to create a project. ...
- Install modules. ...
- Create our Server. ...
- Create Configuration File (.env) ...
- Create Route for Generating JWT. ...
- Create Route for Validating JWT. ...
- Run Server node index.js. ...
- Send Requests and Get Output.
Basically, JWT is a token format. OAuth is an standardised authorization protocol that can use JWT as a token. OAuth uses server-side and client-side storage. If you want to do real logout you must go with OAuth2.
- First, remember that JWTs are tokens that are often used as the credentials for SSO applications. ...
- Grab a JWT you want to decode, or a JWS or JWE containing a JWT. ...
- Input the token.
- Press the Decode button.
- Read the decoded outputs for the header and payload!
- From the navigation menu, select Applications.
- On the Applications page, select your application and then select the Details tab.
- Make note of the Client ID and retrieve the Client Secret from your tenant administrator.
Where is the user data stored after decoding it from the token?
the data is stored in state and not in localstorage due to security issues.
Bearer Tokens are the predominant type of access token used with OAuth 2.0. A Bearer Token is an opaque string, not intended to have any meaning to clients using it. Some servers will issue tokens that are a short string of hexadecimal characters, while others may use structured tokens such as JSON Web Tokens.
It depends on the algorithm(s) used. (Note that JWT supports signing as well as encryption - signed JWTs are the more common use case; my answer is general.) The symmetric key algorithms (AES, HMAC) are the least expensive (very fast).
JWTs can be either signed, encrypted or both. If a token is signed, but not encrypted, everyone can read its contents, but when you don't know the private key, you can't change it. Otherwise, the receiver will notice that the signature won't match anymore.
JWT decode only look for public part so it is totally safe to do that in your front-end code.
- First, remember that JWTs are tokens that are often used as the credentials for SSO applications (mostly for OAuth 2.0). ...
- Fill out the header. ...
- Fill out the payload. ...
- Fill out the signature with either an RSA Private Key for RS56 or HS256 passcode. ...
- Press the Encode button.
- Enjoy your newly created JWT.
If the userID is in the "sub" claim, you can receive it in the following way using this library: Long userID = Long. parseLong(Jwts.
JWT is created with a secret key and that secret key is private to you which means you will never reveal that to the public or inject inside the JWT token. When you receive a JWT from the client, you can verify that JWT with this that secret key stored on the server.
Short answer. JWTs are a convenient way to encode and verify claims. A Bearer token is just string, potentially arbitrary, that is used for authorization.
- Introduction. Creating a user registration form employs the management of the registered user. ...
- Goal. This tutorial helps you: ...
- Prerequisites. You have installed the following: ...
- Set Up a Mongo Database. ...
- Set Up the Server. ...
- Connect to the Database. ...
- Create User Schema. ...
- Perform CRUD Operations.
How do I pass the authorization header in node JS?
In the URL field enter the address to the users route of your local API - http://localhost:4000/users . Select the "Authorization" tab below the URL field, change the type to "Basic Auth" in the type dropdown selector, enter test into the "Username" field and test into the "Password" field.
JSON Web Token – or JWT (pronounced 'jot') – is an access token standard used by applications to create signatures of data sent across the web. It can also encrypt payloads on JSON sent, where tokens are either signed using a private or public/private secret key.
- Step 1: Create the Required Directories.
- Step 2: Create your First App Express API.
- Step 3: Creating the User Module.
- Step 4: Creating the Auth Module.
- Step 1 - Create a directory and initialize npm. ...
- Step 2 - Create files and directories. ...
- Step 3 - Install dependencies. ...
- Step 4 - Create a Node. ...
- Step 5 - Create user model and route. ...
- Step 6 - Implement register and login functionality.
PASETO, or Platform Agnostic Security Token is one of the most successful designs that is being widely accepted by the community as the best-secured alternative to JWT.
Again, API Keys and OAuth2 Access Tokens are both forms of Bearer Tokens. JWT, SAML2, or IBM LTPA2 tokens could be used as OAuth2 Access Tokens or API Keys, but one doesn't usually see the last two used for either purpose.
OAuth2 is very flexible. JWT implementation is very easy and does not take long to implement. If your application needs this sort of flexibility, you should go with OAuth2. But if you don't need this use-case scenario, implementing OAuth2 is a waste of time.
Remember, once a JWT (JSON Web Token) is stolen, it can be the worst thing for an individual and the enterprise as there's a huge chance of data breach and exploitation.
JWTs can be used as an authentication mechanism that does not require a database. The server can avoid using a database because the data store in the JWT sent to the client is safe.
The visualizer in Postman allows us to create and use a Handlebars template to render an HTML table based on the decoded JWT data. Add the following script under the Test tab of your authentication request to decode the JWT token locally. To view the render HTML click on the Visualize tab under the response section.
How do I get JWT tokens from API?
- Basic Flow. Initiate an HTTP request using API Credentials and get your JWT token. ...
- Generating a Token. Once you have the credentials set up, you may make an HTTP POST request to generate your app JWT. ...
- The Received Token. You will then get a response in the following format: ...
- Token Expiration Date.
Figure 1 shows that a JWT consists of three parts: a header, payload, and signature. The header typically consists of two parts: the type of the token, which is JWT, and the algorithm that is used, such as HMAC SHA256 or RSA SHA256. It is Base64Url encoded to form the first part of the JWT.
To use the refresh token, make a POST request to the service's token endpoint with grant_type=refresh_token , and include the refresh token as well as the client credentials if required.
Access tokens are what the OAuth client uses to make requests to an API. The access token is meant to be read and validated by the API. An ID token contains information about what happened when a user authenticated, and is intended to be read by the OAuth client.
In short, you need to use REFRESH_TOKEN when ACCESS_TOKEN expires to get a new ACCESS_TOKEN. JWT has two kind of tokens: ACCESS_TOKEN and REFRESH_TOKEN.
jwt-decode is a small browser library that helps decoding JWTs token which are Base64Url encoded. IMPORTANT: This library doesn't validate the token, any well formed JWT can be decoded. You should validate the token in your server-side logic by using something like express-jwt, koa-jwt, Owin Bearer JWT, etc.
In the URL field enter the address to the users route of your local API - http://localhost:4000/users . Select the "Authorization" tab below the URL field, change the type to "Basic Auth" in the type dropdown selector, enter test into the "Username" field and test into the "Password" field.
- // If you need to convert to Base64 you could do so using Buffer:
- console. log(Buffer. from('Hello World!'). toString('base64'));
- // Reverse (assuming the content you're decoding is a utf8 string):
- console. log(Buffer. from(b64Encoded, 'base64'). toString());
Bearer Tokens are the predominant type of access token used with OAuth 2.0. A Bearer Token is an opaque string, not intended to have any meaning to clients using it. Some servers will issue tokens that are a short string of hexadecimal characters, while others may use structured tokens such as JSON Web Tokens.
- From the navigation menu, select Applications.
- On the Applications page, select your application and then select the Details tab.
- Make note of the Client ID and retrieve the Client Secret from your tenant administrator.
Where is the user data stored after decoding it from the token?
the data is stored in state and not in localstorage due to security issues.
- First, remember that JWTs are tokens that are often used as the credentials for SSO applications (mostly for OAuth 2.0). ...
- Fill out the header. ...
- Fill out the payload. ...
- Fill out the signature with either an RSA Private Key for RS56 or HS256 passcode. ...
- Press the Encode button.
- Enjoy your newly created JWT.
- Step 0 — Setup Express JS app. ...
- Step 1 — Register a new User. ...
- Step 2 — Authenticate Users and return JWT tokens. ...
- Step 3 — Understanding the accessToken and refreshToken model. ...
- Step 4 — Retire Refresh Tokens.
- Introduction. Creating a user registration form employs the management of the registered user. ...
- Goal. This tutorial helps you: ...
- Prerequisites. You have installed the following: ...
- Set Up a Mongo Database. ...
- Set Up the Server. ...
- Connect to the Database. ...
- Create User Schema. ...
- Perform CRUD Operations.
Explanation: The first middleware is used for checking the authentication of the client when the server start and the client enter the localhost address. Initially req. headers. authorization is undefined and next() callback function return 401 status code unauthorized access to the browser.
If you pass a string containing characters that cannot be represented in 8 bits, it will probably break. Probably that's why btoa is deprecated. atob(): returns a string where each character represents an 8-bit byte. Otherwise, you could install buffer with "yarn add buffer" or "npm i buffer" to run on browser.
atob() The atob() function decodes a string of data which has been encoded using Base64 encoding. You can use the btoa() method to encode and transmit data which may otherwise cause communication problems, then transmit it and use the atob() method to decode the data again.
The easiest way to encode Base64 strings in Node. js is via the Buffer object. In Node. js, Buffer is a global object which means that you do not need to use require statement in order to use Buffer object in your applications.
Bearer tokens enable requests to authenticate using an access key, such as a JSON Web Token (JWT). The token is a text string, included in the request header. In the request Authorization tab, select Bearer Token from the Type dropdown list. In the Token field, enter your API key value.
REST Assured Tutorial #16 - Bearer Token Authentication in ... - YouTube
How does a bearer token look like?
Bearer Tokens are the predominant type of access token used with OAuth 2.0. A Bearer Token is an opaque string, not intended to have any meaning to clients using it. Some servers will issue tokens that are a short string of hexadecimal characters, while others may use structured tokens such as JSON Web Token.